So what we’ve just done for converting a subnet mask to a wildcard mask was relatively simple. The scenario we presented was relatively simple as well, but is it always going to be that simple? No, we now want to filter for multiple subnets, look at the example we have here. We have 172.30.16.0/24 through 172.30.31.0/24, they are multiple subnets, not just one anymore. Things are little more complicated now, aren’t they?
They absolutely are, I count 16 unique subnets. If you look at this, you’re like, how do I get 16, it looks like 15. Well don’t forget it’s inclusive of the first value, so if you found 15, that’s just the delta between the first and the last, okay, but wait a minute. Let’s move to our second step here, let’s look at the second step. We’ve got an entry in an access control list that would capture 16 different subnets and there’s a benefit to this. I could have an access list that had 16 different individual subnets matched in just discreetly, line by line.
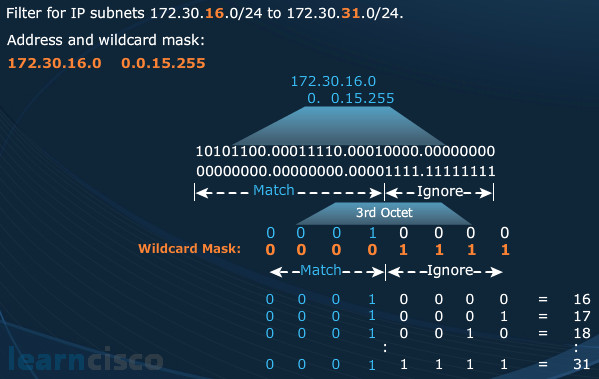
But if I can compress that, if I can summarize those entries and the logic of them, that makes my access list easier to read, it makes it easier for the device to process it. So there is a benefit to doing this sort of approach. So I see my wildcard mask here and this is a tricky one. It’s 0.0.15.255. How do we interpret 0.0.15.255? Where did that come from?
Certain bits of that IP address we will ignore. So we have to figure out from a binary standpoint, what has to match and what has to be ignored. That’s a lot of work and we do not like using binary if we don’t have to. But if you focus on the binary example here, you’ll see that, with the .15 in the third octet for our wildcard mask and the .255 in the fourth octet, you’ll see what’s ignored and what’s matched and how it all works out perfectly. All right, it’s nice on paper, but how do we do it under pressure? How we do it fast? How do we make it count when it has to count? Do we have a shortcut for this as well? We do!
This shortcut is one of my favorites, we are doing raw subtraction this time. Let’s find what we classify as the significant octet. What is that significant octet where our major changes are happening? Look at the third octet going from 16 to 31. Let’s do some subtraction on this octet, 31 minus 16, what does that equal? 15! Let’s take that value and put it in the third octet of the wildcard mask and then everything before that we will put as zeroes, everything after that, we will put as ones in binary. And when you convert it all, you end with 0.0.15.255.
Isn’t that what we were just shown the long way using binary? Yes it was, and we just did it here instantaneously in our heads. No paper, no calculators, just easy subtraction. It seems almost too good to be true, but really, remember it’s a range operator, which also is sort of like a delta between starting and ending. We are finding the delta, it’s 15, which matches one of those expected values in a wildcard mask. So here you go, this is basically the final approach to being absolutely at the expert level of wildcard masks, the only thing we don’t teach you here is how to find odds and evens. And that’s something that’s saved for maybe two years down the road.
Wildcard bit mask abbreviations
We still have not covered the full syntax of an access control list. That’s all right, we will be there shortly, but we can do shortcuts. Instead of having to type out the full address and wildcard mask, there are a few shortcuts that we can use to avoid having to type out the long address in wildcard mask combination. For example, if we want to match a specific address and that address only, 172.30.16.29, what would be the appropriate wildcard mask to match that specific address? Well, if I’m trying to match every bit of an IP address, my wildcard mask would have to be all zeros, match every bit perfectly.
But there’s a shortcut for that, we can type in “host“, so when we craft the access control list, we could type in “host 172.30.16.29” and it would mean 172.30.16.29 0.0.0.0, just a shortcut. What about every possible IP address, what combination would we have there? Well just think about it as a range operator, a range. Starting IP and ending IP, what’s the starting IP of every address? 0.0.0.0. What’s the ending IP if we are trying to consume every possible IP address? It will be 255.255.255.255, the minimum and the maximum. So our address and wildcard mask combination would be 0.0.0.0 255.255.255.255, just do the addition. Put 0.0.0.0 over top of 255.255.255.255 and then the result will be starting IP – all zeros, ending IP – all 255s.
That’s a lot of typing. If you want to include everything, the keyword shortcut for that is “any“. We use it often, we use it often in the real world when we are trying to encompass all the other IP addresses. Of the two that I use, I typically use the any keyword way more than the host keyword because I am just used to putting in my IP address and then choosing my wildcard mask. And the host sequence, the host keyword, I actually have to go back and backtrack to the previous parameter, insert host. It’s not a good workflow for me, but it’s important to know because that’s the way that the IOS will represent it in your running config. It will say host even if you enter it with an all zeros wildcard mask. But any, that’s a way to save your fingers some extra keystrokes, it is definitely a good thing.
Our Recommended Premium CCNA Training Resources
These are the best CCNA training resources online:
Click Here to get the Cisco CCNA Gold Bootcamp, the most comprehensive and highest rated CCNA course online with a 4.8 star rating from over 30,000 public reviews. I recommend this as your primary study source to learn all the topics on the exam.

Want to take your practice tests to the next level? AlphaPreps purpose-built Cisco test engine has the largest question bank, adaptive questions, and advanced reporting which tells you exactly when you are ready to pass the real exam. Click here for your free trial.
