VLANs are pretty simple in concept and in practice. The following list hits the high points:
- A collision domain is a set of network interface cards (NICs) for which a frame sent by one NIC could result in a collision with a frame sent by any other NIC in the same collision domain.
- A broadcast domain is a set of NICs for which a broadcast frame sent by one NIC is received by all other NICs in the same broadcast domain.
- A VLAN is essentially a broadcast domain.
- VLANs are typically created by configuring a switch to place each port in a particular VLAN.
- Layer 2 switches forward frames between devices in the same VLAN; they cannot forward frames between different VLANs.
- A Layer 3 switch, multilayer switch, or router can be used to essentially route packets between VLANs.
- The set of devices in a VLAN typically also is in the same IP subnet; devices in different VLANs are in different subnets.
When using VLANs in networks that have multiple interconnected switches, you need to use VLAN trunking between the switches. With VLAN trunking, the switches tag each frame sent between switches so that the receiving switch knows to what VLAN the frame belongs. Here is the basic idea:
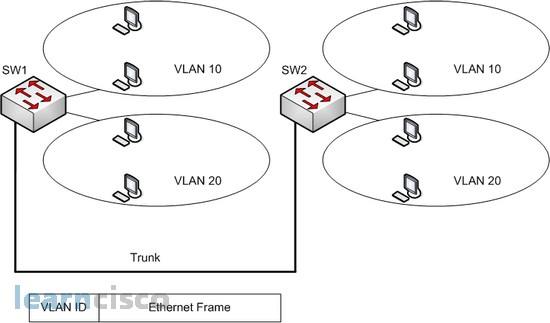
With trunking, you can support multiple VLANs that have members on more than one switch. For instance, when Switch 1 receives a broadcast from a device in VLAN 1, it needs to forward the broadcast to Switch 2. Before sending the frame, Switch1 adds another header to the original Ethernet frame; that new header has the VLAN number in it. When Switch 2 receives the frame, it sees that the frame was from a device in VLAN1, so Switch 2 knows that it should only forward the broadcast out its own interfaces in VLAN1.
Cisco switches support two different trunking protocols-Inter-Switch Link (ISL) and IEEE 802.1Q. Both provide basic trunking, but they have some differences.
ISL
Cisco created ISL before the IEEE standardized a trunking protocol. Because ISL is Cisco proprietary, it can be used only between two Cisco switches. ISL fully encapsulates each original Ethernet frame in an ISL header and trailer. The original Ethernet frame inside the ISL header and trailer remains unchanged.
The ISL header includes several fields, but most importantly, the ISL header VLAN field provides a place to encode the VLAN number. By tagging a frame with the correct VLAN number inside the header, the sending switch can ensure that the receiving switch knows to which VLAN the encapsulated frame belongs. Also, the source and destination addresses in the ISL header use MAC addresses of the sending and receiving switch, as opposed to the devices that actually sent the original frame.
802.1Q
The IEEE standardizes many of the protocols relating to LANs today, and VLAN trunking is no exception. After Cisco created ISL, the IEEE completed work on the 802.1Q standard, which defines a different way to do trunking.
802.1Q uses a different style of header than does ISL to tag frames with a VLAN number. In fact, 802.1Q does not actually encapsulate the original frame. Rather, it adds an extra 4-byte header to the original Ethernet header. That additional header includes a field with which to identify the VLAN number. Because the original header has been changed, 802.1Q encapsulation forces a recalculation of the original FCS field in the Ethernet trailer, because the FCS is based on the contents of the entire frame.
Both ISL and 802.1Q provide trunking. The header used by each varies, and only ISL actually encapsulates the original frame, but both allow the use of a 12-bit-long VLAN ID field. So, either works fine, and both support the same number of VLANs because both use a 12-bit VLAN Number field. ISL and 802.1Q both support a separate instance of spanning tree for each VLAN. ISL supported this feature much earlier than did 802.1Q, so in years past, one of the stated differences between the two trunking protocols was that 802.1Q did not support multiple spanning trees.
A key difference between ISL and 802.1Q relates to a feature called the native VLAN. 802.1Q defines one VLAN on each trunk as the native VLAN; by default, this is VLAN 1. By definition, 802.1Q simply does not encapsulate frames in the native VLAN when sending the frames over the trunk. When the switch on the other side of the link receives a frame in the native VLAN, it notices the lack of an 802.1Q header and knows that the frame is part of the native VLAN. Native VLANs play a very important role from a practical perspective. Imagine that you have many PCs connected to some switch ports, and those PCs do not understand 802.1Q. You also plan to install IP phones near those PCs. IP phones have a built-in switch so that you can connect the phone to the Ethernet cable from the switch and then connect the phone to a PC. The phone understands 802.1Q, so you can put the phone in one VLAN and the PC in another. You can configure all those ports for 802.1Q, placing the PCs in the native VLAN. They work fine when connected directly to the switch, because the switch does not use any encapsulation for the native VLAN. When you install an IP phone between the switch and the PC, the phone can understand the 802.1Q headers and can send and receive traffic to and from the switch. The phone can just pass the native VLAN traffic between the PC and the switch.
Something else, if you want to be sure that you will have interoperability between different vendor devices, you must use 802.1Q encapsulation.
Our Recommended Premium CCNA Training Resources
These are the best CCNA training resources online:
Click Here to get the Cisco CCNA Gold Bootcamp, the most comprehensive and highest rated CCNA course online with a 4.8 star rating from over 30,000 public reviews. I recommend this as your primary study source to learn all the topics on the exam.

Want to take your practice tests to the next level? AlphaPreps purpose-built Cisco test engine has the largest question bank, adaptive questions, and advanced reporting which tells you exactly when you are ready to pass the real exam. Click here for your free trial.
