In talking about security, we have to come to terms with the fact that we no longer live in a closed network environment. This is not even driven by security; it is driven by cost and flexibility, and our desire and need to interact with the rest of the world. In a closed network, these lines and technologies, like Frame Relay and the traditional PSTN, were designed for a specific purpose, and not necessarily to hold multimedia traffic, and to allow for the richness of transmissions that we’ll require today. They are also designed and built with their own characteristics in mind, and not necessarily integration with other technologies.
The security reality in a closed network is a lot more controllable. We are not subject to external attacks because we are confined within the quiet and relaxed environment of our own network. Internal incidents are easy to contain, because they will remain internal with no connectivity to the external world.
Open Networks
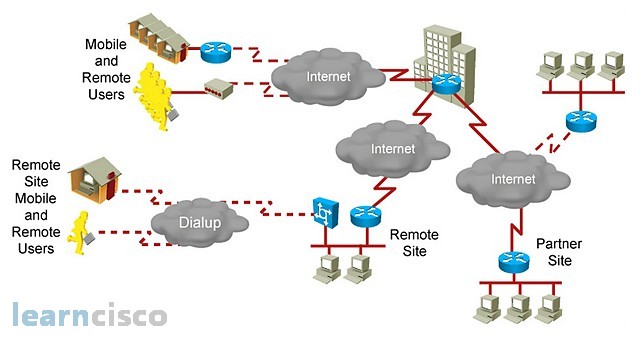
This is not the case in today’s networks, though. The name of the game is public networks and global connectivity with the networks, like the Internet as the ultimate example of the public network. We have mobility requirements and we have flexibility requirements. This is a world of integrated systems and it is a world of integrated standards where we want to have transparency of connection, at the same time mobility and universal access, and at the same time ease of management of the whole infrastructure. This will open the door to security concerns. Obviously, using a public network that everybody else uses will result in confidentiality concerns, also integrity concerns, also privacy concerns. The more we offer services to the rest of the world, the more the malicious minds of the world will have access to those services and work toward surprising us with a newer and more efficient forms of exploiting our assets.
Adversaries and Classes of Attack
The attacker has a different profile nowadays. Not only are we talking about script kiddies with a lot of time on their hands, but we are talking about competitors as potential attackers, criminals, organized crime, terrorists, and nation-states. Their motivations may vary, but one common motivation is now financial motivation, and every time money is involved, things like greed and avarice will come into play, and we know how powerful those motivations are. Disgruntled employees will have anger and revenge in mind, but again, the financial aspect and the greed aspect is a strong driver to newer security strategies. All of these results in different classes of attacks. No longer is the active attack of bringing down a site or actively looking for connections and proprietary information. The one that will have a greatest impact, a simple passive attack monitoring a sniffing traffic, and sniffing and enumerating networks, will serve the purposes of stealing information in the form of corporate assets or simply private personal information. Some incidents may not even be considered attacks, and are typically performed by insiders, employees, or members of the family that simply make mistakes and are able to exploit an already vulnerable infrastructure.
Common Threats
Very frequently, we see newer technologies and methods to exploit networks. The threats can be classified in certain categories in order to study them, and be able to protect against them, and design sound security infrastructures. But again, this changes frequently. The anatomy of a typical attack may include reconnoissance tools to learn information about target networks, enumerate the topology and the services in the network, and/or simply use readily available information available on the Internet about servers, services, and companies. This is typically followed by an access attack once I know what the network looks like. Then, let me try to retrieve data from it, gain supervisor access into servers and computers, and escalate their access privileges to dig deep into their network and obtain more valuable information. Password attacks can be considered a subset of an access attack, and trying to gain access and retrieve data by exploiting and understanding the password structure, and using valid passwords to enter a network. If we add to this all of the physical threats like natural disasters, hardware threats, failures of the power grid, and even maintenance threats, then this becomes a grim scenario.
Password Attack Threat Mitigation
If we look a little closer in one of the subsets of an access attack, for example, password threats, then we realize that the methods being used by the “bad guys” are highly sophisticated. They will try to exploit and look into the password database and crack all passwords. It will try to use key stroke loggers to simply monitor all the key strokes that we type, and gather our passwords from there. Or, they may even use social engineering, simply calling you and asking you for your password while pretending to be a network administrator, and from there to go dumpster diving and look for your credit card statements in your garbage. Clever mitigation techniques are needed anywhere, from a good strategy in terms of the use of strong passwords using upper case, lower case, numbers, and special characters. We have a specific and minimum password length to policies that relate to reaction to attacks in the form of disabling accounts and account lockout after a certain number of unsuccessful login attempts, to the use of two- factor authentication and strong authentication, token cards, smart cards, and digital certificates to authenticate users into the network.
Our Recommended Premium CCNA Training Resources
These are the best CCNA training resources online:
Click Here to get the Cisco CCNA Gold Bootcamp, the most comprehensive and highest rated CCNA course online with a 4.8 star rating from over 30,000 public reviews. I recommend this as your primary study source to learn all the topics on the exam.

Want to take your practice tests to the next level? AlphaPreps purpose-built Cisco test engine has the largest question bank, adaptive questions, and advanced reporting which tells you exactly when you are ready to pass the real exam. Click here for your free trial.
