We can see switch security in multiple dimensions. One of them is physical and environmental and within that there are several categories and classifications. Those are listed here. Hardware threats are those related to physical damage to the equipment, mishandling could be a cause of this and notice this is not necessarily a malicious incident; it can simply come from poor change management or poor policies in terms of physical installations. Also, lack of policy in terms of handling of the equipment. Environmental threats are those related to extreme temperatures and humidity. A good data center and wiring closet design following best practices in terms of physical location, cooling, etc., will help mitigate these threats.
Electrical threats are maybe a lot more common any where from voltage spikes to unconditioned power to complete and full power loss. These could be mitigated with UPS-type solutions. Maintenance threats are more related to the methodology and the process to not only handle, but design, the physical location of equipment. So poor cabling could be a security threat if it will cause an electrical problem or if it would cause a hardware threat by just dropping equipment due to poor cabling. Lack of critical spare parts could also be a maintenance threat, which demonstrates poor design and planning in terms of the levels of redundancy for equipment.
Configuring a Switch Password
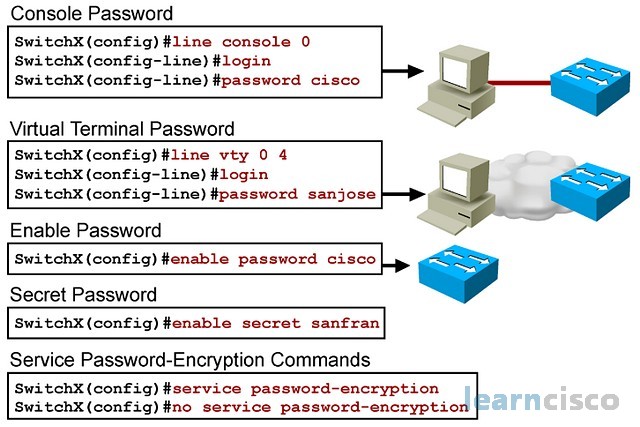
Other threats could be related to authentication and identity management; that is why we set up passwords and provide access control with the use of passwords. A basic password setup could be related to specific lines or lines of access into the switch, for example, the console, the VTY lines, which are related to terminal access into the equipment. These would rule Telnet and SSH access, but once you are connected to the equipment via console or Telnet, then you could be able to access the privilege mode with the enable password and so that is another thing we have to consider. One thing common to all these passwords is that they are set and fixed per line or per function like the enable password.
SwitchX(config)#no aaa new-model
SwitchX(config)#line console 0
SwitchX(config-line)#login
% Login disabled on line 0, until ‘password’ is set
SwitchX(config-line)#password cisco
SwitchX(config-line)#exiSwitchX(config)#line vty 0 4
SwitchX(config-line)#login
% Login disabled on line 2, until ‘password’ is set
% Login disabled on line 3, until ‘password’ is set
% Login disabled on line 4, until ‘password’ is set
% Login disabled on line 5, until ‘password’ is set
% Login disabled on line 6, until ‘password’ is set
SwitchX(config-line)#password sanjose
SwitchX(config-line)#exiSwitchX(config)#enable password cisco
SwitchX(config)#enable secret sanfran
SwitchX(config)#service password-encryption
Another more advanced way to do this would be to tie this to either local or central users, so that you can start deploying a role-based access control type management of the device. Commands listed here set up passwords for the lines. You would first have to enable the authentication process on the line with the command, but then use a command to set it. Then will simply set up that password unencrypted whereas there is an enhancement to the enable password that will encrypt or hide that password using specific hashing mechanisms. Other than the enable secret, all other passwords are clear text and will be displayed like that in the show running and show startup configuration commands. If you want to hide the commands and encrypt them with very basic encryption, you can use the last command. After you type in this command, then all new passwords will be encrypted; you can disable the function with a no version of the command.
Configuring the Login Banner
Login banners help in conveying a certain message to users authenticating to the switch; it can serve the purpose of displaying information and also displaying the policy for unauthorized access and the sources of support in the case of missing passwords or blocked accounts. You can set up that banner with the command.
Notice that the way it works is that you would issue the banner login command followed by the termination character or delimiting character.
Telnet vs. SSH Access
Telnet has historically been the most common option to connect two routers for management purposes and also to switches. It is, however, insecure in that it provides no confidentiality or integrity to the connection. In other words, a sniffer could collect enough packets to determine not only what you are doing in terms of commands but also steal your passwords; passwords will not be encrypted. The use of SSH is an improvement to this. Both SSH version 1 and version 2 will encrypt the transactions and will serve also the purpose of connecting to the device for configuration management purposes. SSH version 2 perhaps having a more enhanced secured encryption algorithm. If you want to use SSH, you would have to create keys for encryption and you would have to use command.
In order to create keys, those keys are tied to or contained a domain name, so that is why you need that command. Set up the DNS domain name for the switch. As an option to line authentication or line passwords, you can also define a local user database; you define users with the command. Those would be local to the switch and then tie your lines of access to local database with the login local command. A more advanced configuration would use AAA, authentication authorization and accounting servers, to centralize the user database and provide economies of scale for multiple devices, sharing the same user database from the central server.
Configuring Port Security
Another security control available in switches like the Catalyst 2960 Series is port security. This feature allows you to create a boundary to the number of MAC addresses you can learn on a port and also identify actually which MAC addresses you allow in a certain port. This is effectively layer 2 security and it aids in physical security and allows you to define strategies in terms of who can connect to a particular switch port and how many machines can connect to that port.
The configuration is fairly straightforward. It starts with this command at the interface configuration level, , followed by certain keywords that allow you to customize and tune the way the feature works. Let us take a look at some of those options by looking at a standard example configuration. The scheduler configuring for interface fa0/5, the first thing you need to do is enable the port as an access port, as opposed to a trunk port. An access port is the one that connects to endpoints like workstations and laptops. The second step is to enable port security with that command; even though the other command starts port security, you actually have to enable the feature with switchport port-security enter and no other keywords. The third step is to define the maximum number of MAC addresses, with the same command, switchport port-security, maximum 1 means you are going to allow only one MAC address to connect and be learned through that port.
Switch(config)#interface fa0/5
Switch(config-if)#switchport mode access
Switch(config-if)#switchport port-security
Switch(config-if)#switchport port-security maximum 1
Switch(config-if)#switchport port-security mac-address sticky
Switch(config-if)#switchport port-security violation shutdown
As we know, switches learn MAC addresses, and so this is going to be dynamic. Once a switch learns a MAC address, it will not accept anything beyond that maximum number, and with that you can play with one or more. You can actually say five, ten, and determine the number of machines that can connect to port. If a switch reloads, those MAC addresses are forgotten. So if you want to remember them, across switch reloads, you would have to make them sticky with this keyword here.
So with that and with a machine connected to the port, the switch would learn the MAC address dynamically and then that MAC address would become commands on the configuration file of the switch. And then you would have them and remember them across bootups. Finally, you need to define the action you want to take upon violation of the maximum limits. You have several options with this keyword violation you can find shutdown, which would effectively shut down the port, which would require manual intervention of the administrator to enable the port again. But you have several other options like disabling the port temporarily or actually leave the port enabled but send a syslog message so that administrators know that the limits have been reached.
After port security has been configured, you could display the settings and the status with the command. You can do it for all interfaces or for specific interfaces like in this example, and you can also use the address keyword to actually display the secured MAC addresses per the interface. This is the basic command that will display whether port security is enabled on the interface and the status of it. In this case, secure up means that no security violations have occurred. Violation mode though is shut down and so as soon as an unknown MAC address or MAC address goes beyond the limits and the port is connected, then the switch port will be shut down.
Here is the aging time, where a value in minutes is specified for registered MAC addresses, to be able to time out entries without having to manually remove them. The aging time in this case is absolute. Finally, the number of MAC addresses and the total current MAC addresses that the port has learned. Sticky configurations will also be displayed and the number of security violations that have occurred on the switch port.
Securing Unused Ports
Best practices call for securing the unused ports on a switch that can create a security hole because again ports will be enabled by default. If you have DHCP on a certain network and are not providing physical security or your physical security may not have consistent policies, then you could allow unwanted access into the network. The best practice is to disable the interfaces for unused ports.
For that we use a shutdown command by going into the interface configuration mode and setting down specific interfaces. In more recent version of the IOS operating system, you will find the option to include ranges of interfaces and go into a range configuration mode and shut down multiple interfaces at the same time. Remember, you can enable the interface again by issuing the no version of the command. In other words, shutdown would administratively disable the interface; no shutdown will administratively enable the interface.
Our Recommended Premium CCNA Training Resources
These are the best CCNA training resources online:
Click Here to get the Cisco CCNA Gold Bootcamp, the most comprehensive and highest rated CCNA course online with a 4.8 star rating from over 30,000 public reviews. I recommend this as your primary study source to learn all the topics on the exam.

Want to take your practice tests to the next level? AlphaPreps purpose-built Cisco test engine has the largest question bank, adaptive questions, and advanced reporting which tells you exactly when you are ready to pass the real exam. Click here for your free trial.
