In this lesson, we are going to describe its features, main elements, and general operations of Cisco Software Device Manager (Cisco SDM). The highlight will be the use of wizards, to streamlined configuration and hide the complexity of commands.
What is Cisco SDM?
SDM (Security Device Manager) is a web-based device management tool for Cisco IOS routers. It includes several functions that point to ease of management, standard interfaces, interoperability, and security. The first thing to highlight is that it is embedded. That means it is a series of HTML files and other formats that will be included in the router’s flash memory, so all you have to do is point your browser to an active IP address of the router and if SDM support is enabled, then you will obtain a graphical user interface menu-driven point and click type configuration.
It therefore hides the complexity of commands and command-line interfaces from the administrators, allowing for a faster deployment and easier troubleshooting and monitoring. It is driven by wizards, which allow you to simply answer questions and create a whole configuration for a specific function. It will also have tools for the power administrator who requires editing ACLs, the good old ACLs, and those administrators that still rely on configuration components and commands to do more advanced troubleshooting and monitoring.
Cisco Router and Security Device Manager
This is how it looks like. You simply point your browser using the regular HTTP into an active IP address of the router. For confidentiality, integrity, and endpoint authentication, you would use HTTPS and rely on the secure sockets layer for secure management. The home page is a dashboard-type application. It will include general information about the router, including the model type, available resources, and feature availability.
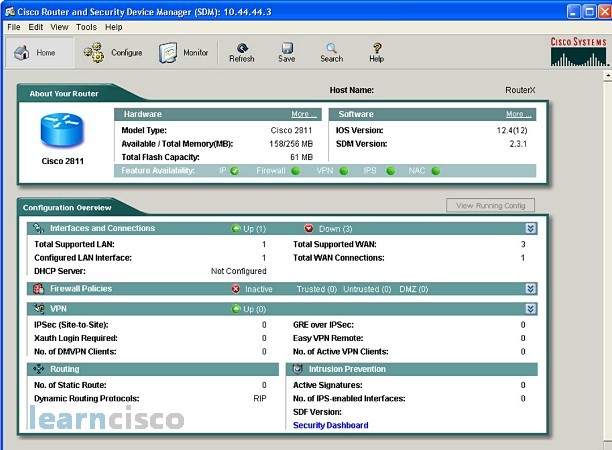
In this example, we have a router that has not only IP features but also acts as a firewall as a VPN and so on. Specific components and functions are included in the dashboard, not only for a general management of interfaces and DHCP, but also for specific security functions. Here we see that the firewall policies are inactive and so even though the router has firewall capabilities, they are either disabled or not configured. You can also see live information in terms of the number of IPsec tunnels and active VPN clients currently connected to the router.
Supported Cisco Routers and Cisco IOS Software Releases
SDM is an embedded component, but a standalone component. You can upgrade the software without having to upgrade the whole operating system of the router. If you issue the show version command on your router, then you will see the version of IOS and the version of SDM. This version again can be upgraded; new files can be copied in the flash memory of the router and, therefore, new IOS versions and commands can be supported.
The application itself is supported in a number of Cisco router platforms including the ISR family. The latest releases are recommended if you want to support the latest releases of IOS and the latest command sets. Compatibility between IOS and SDM is important; in fact, certain versions of SDM will not work with the certain versions of IOS. One of the reasons for this is due to the fact that SDM will generate commands and it has to generate them for specific versions of IOS.
Configuring Your Router to Support SDM
Holding the SDM files in flash is not enough; you have to enable and configure access to the application on the router. These are the steps. You would have to enable the router as an HTTP or HTTPS server depending on whether you are providing confidentiality or not. You could, in fact, create policies that accept connections on HTTP, but then map the port into HTTPS and negotiate an encrypted transaction; the required commands for this step are listed here:
!
ip http server
ip http secure-server
ip http authentication local
!
The next step is to create user accounts for SDM access. When administrators connect via their browser, they will be prompted for this user name and password. The user accounts need to be of privilege level 15, which is the highest privilege level and it contains the same permissions as your privileged mode in CLI. Remember, you enter privileged mode when you type the command enable. The last step is to enable SSH and Telnet for local login and privilege level 15.
SDM Startup
SDM runs as a Java applet in your browser, so you first point your browser to an active IP of the router. The SDM home page appears in the browser window and the User name and password dialog box will also appear. If you are able to log in with the user name and password of the account with privilege level 15, then the SDM JAVA applet will begin the loading to your PC.
SDM is a signed Java applet, and this may cause your browser to display a security warning. You can accept the certificate for this session or you can always accept the certificate and for any upcoming session, but these options will vary depending on the browser you are using. After successful authentication, you will be ready to go into the dashboard home page.
Cisco SDM Wizards
The wizard-based configuration provides ease of administration and management, streamlines the process, and it allows users with no IOS CLI proficiency to manage and monitor the device. Most of the options have some sort of wizard associated with them. Some of them are related to interfaces and connections, but others are related to specific security functions, in case in point the security audit option, which has features to run a security audit according to different best practices and according to your own input and also a feature or option to do a one button router lock down, which again complies with certain specifications and security policies. You can also automate the deployment of signatures including custom signatures for intrusion prevention systems with the IPS wizard.
In summary, SDM is a powerful tool for configuring Cisco routers. It contains easy-to-use wizards for efficient configuration and allows you to customize the configuration with certain advanced features.
Our Recommended Premium CCNA Training Resources
These are the best CCNA training resources online:
Click Here to get the Cisco CCNA Gold Bootcamp, the most comprehensive and highest rated CCNA course online with a 4.8 star rating from over 30,000 public reviews. I recommend this as your primary study source to learn all the topics on the exam.

Want to take your practice tests to the next level? AlphaPreps purpose-built Cisco test engine has the largest question bank, adaptive questions, and advanced reporting which tells you exactly when you are ready to pass the real exam. Click here for your free trial.
