Well, as we learn from the first module, networks are getting much more complex and our devices offer a wide variety of services that meet our business needs, and business continuity needs several features and services to ensure the availability under all circumstances. Now connecting to the Internet is pretty much a must-have. So the network devices and infrastructure are going to be exposed to a lot of risks and a lot of threats on a daily basis. So putting together some best practices will help secure your network foundation by protecting network elements and their interactions. In the Internet environment and the cloud computing environment to name a couple, best practices are going to mean distrusting every single packet basically and implementing policies aimed at categorizing traffic. Then different traffic classes will be processed under different policies to make sure that not only forwarded properly but also they’re protected adequately.
Threats against network infrastructure
Okay, here is a list of some common threats to our network infrastructure.
- Design errors
- Protocol weaknesses
- Software vulnerabilities
- Misconfiguration
There are vulnerabilities in the design, the design of applications, the design of systems. There are weaknesses that are inherent in protocols, for example IEEE protocols, open standard protocols. They have those weaknesses because they’re there for interoperability and functionality. So they’re just there, okay. There are also software vulnerabilities. Some of those are by design, some of those are obviously accidental, then the human error and misconfiguration, okay, that’s a biggie.
What are our threats?
- Trust exploitation attacks
- Login, authentication, and password attacks
- Routing protocol exploits
- Spoofing
- Denial-of-service attacks
- Confidentiality and integrity attacks
Well, we’ve got trust exploitation, taking advantage of relationships between systems, and servers, and clients, and servers, for example. You got threats against login, access control, authentication; password attacks – different types of methods for extracting keywords, and passwords, and strings; exploiting routing protocols when there is no authentication in place; spoofing – spoofing IP addresses, spoofing MAC addresses. There are denial-of-service attacks and distributed DOS attacks. There are also attacks against confidentiality to break down cryptosystems, and integrity attacks take advantage of weak hashing mechanisms.
What is the impact?
- Exposed management credentials
- High route processor CPU utilization (near 100 percent)
- Loss of protocol keepalives and routing protocol updates
- Route flaps and major network transitions
- Slow or unresponsive management sessions
- Indiscriminate packet drops
Well, exposing credentials, using up CPU cycles, corrupting your routing table, flapping network transitions and disruptions, slow sessions, indiscriminate packet drops – just to name a few.
We can see from the following diagram that this is a problem that’s going to be affecting our entire network infrastructure. Starting at the top with our edge customer, edge router that connects to our service provider to the Internet.
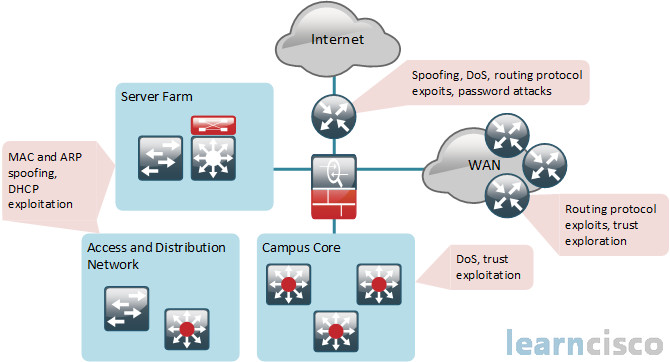
We have IP spoofing, we have denial-of-service attacks, we have routing protocol exploits, for example, if we’re using BGP to our provider. There are also password attacks to try to get through authentication mechanisms and authentication proxies on that perimeter router, or if we’re using authentication in our service provider. If you go down clockwise to the Wide Area Network, same thing there. Routing protocol exploits with our WAN protocols like OSPF, EIGRP, for example; trust exploitation between the peers in the routing protocols and other services, in the Campus Core or we would call our corporate LAN. You’ve got denial-of-service attacks, trust exploitation. Then of course, you’ve got spoofing of MAC addresses, and ARP spoofing, and exploitation of DHCP that can happen not only at the core, but more likely at the Access and Distribution layers of our network in the server farm or datacenter.
Cisco NFP framework
Now in order to implement Network Foundation Protection, you have to understand that your router is typically divided into three functional planes, and actually these aren’t the only planes. There is actually a service plane, but we’re not going to talk about that here in this course. We have the data plane, we have the management plane, we have the control plane.
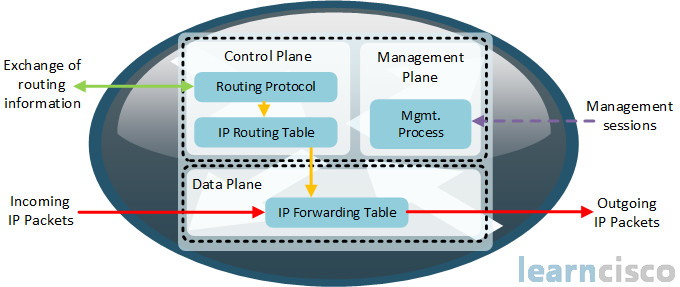
Now, the data plane could be considered transit traffic or customer traffic, and of course, the customer could be a service provider’s customer, or in our organization, the customer are own endusers, our business units, our departments, our buildings on our campus. So the data plane is basically the traffic that is moving through our router – transit traffic that’s being forwarded from one interface to another, and it’s typically 80% or more of our traffic. So we have a route processor there that’s managing certain packets.
The management plane is separate from a functional perspective. This is basically traffic that is directed towards the router. So it’s towards an interface or an IP address on an interface for the purposes of management, okay – either packet-based management or character-based management of that device.
The control plane is basically what controls all the other planes, okay. The control plane is dealing with the actual process of routing traffic through the device. So it could be used by the dynamic routing protocols, for example. Control plane packets would be ARP, BGP, OSPF, EIGRP packets. These are network device-generated or received packets that are for the generation and operation of the network itself. So that’s what we’re talking about with control plane.
The management plane is going to have a lot of protocols like Telnet, Secure Shell, TFTP, SNMP, FTP, NTP. All those protocols are on the management plane. Typically, control plane packets and management plane packets are destined to the router itself on its receive interface to its processor.
We need a well organized, structured approach to protecting the operational planes of our router, and these three functions will benefit if you have a combined effort. You can’t really protect the control plane, and the data plane, and the management plane all by themselves individually. We need a structured approach to protect all three functions. As we know, the control plane will affect our routing of our packets, it implements routing protocol functionality. The management plane affects the ability to configure and monitor and control our device and eventually implement our security control to the management plane. Then the data plane affects the ability to forward traffic, which is a huge percentage of the duties of our router. So by overloading the control plane, you can slow down the routing process, and therefore, you could degrade the other service levels and overall corporate productivity. So packets that traverse the control plane that are destined for the CPU with a router need to be protected, because all packets entering the control plane are actually redirected by the forwarding plane. So you can see they all kind of work together.
Here we can see kind of a simplified explanation of these concepts where the Cisco Network Foundation Protection is going to secure the control plane, which is our ability to route. The management plane, which is the ability to manage, and the data plane, which is the ability to forward, and it’s a secure foundation to protect our device.
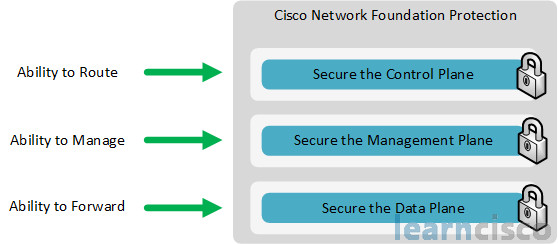
It’s a series of IOS features, which specifically protect the control plane by locking down services and routing protocols, the device data plane for malicious traffic as well as protecting the device management plane.
Cisco NFP toolkit
This table shows us the Network Foundation Protection Toolkit. There are other features and tools that are available but these are the main ones, and we’re going to be discussing most of these and of course, we’ll expand on these as you get into the CCNP security track.
| Plane | Feature | Benefit |
|---|---|---|
| Control Plane | Control Plane Policing (CoPP) | Filter or rate limit control plane traffic with no regard to physical interface |
| Control Plane Protection (CPP) | Extend CoPP with granular traffic classification | |
| Routing protocol authentication | Integrity of routing and forwarding | |
| Cisco AutoSecure | Automate device hardening | |
| Management Plane | Authentication, authorization and accounting (AAA) | A comprehansive framework for role-based access control |
| NTP, Syslog, SNMP, SSH, TLS | Secure management and reporting | |
| CLI views | Obtain the benefits of RBAC for command line access | |
| Data Plane | Access control lists | Traffic filtering consistent across security device platforms |
| Layer 2 controls (private VLANs, STP guards) | Protect the switching infrastructure | |
| Zone-based firewall, IOS IPS | Deployment flexibility in IOS form factor |
But at the control plane, we have the Control Plane Policing which is an older feature. We have a newer CPP – Control Plane Protection which extends CoPP with granular traffic classification. You have Routing Protocol Authentication to guarantee the integrity of routing and forwarding, and you also have the Cisco AutoSecure to protect and harden the control plane. At the management plane, we have AAA services – authentication, authorization, and accounting. We also have a NTP, Syslog, SNMP, Secure Shell, and TLS, and also role-based CLI or views giving you the benefits of a role-based access control for management. At the data plane, we have of course the access control list – the classic mechanism. We also have Layer 2 controls – PV LANs or private VLANs, Spanning Tree Protocol Guards, and others) and then zone-based policy firewall and IOS IPS. These are all features on the integrated services router.
Cisco NFP in action
If we go back to that topology from earlier, we can look at some of our methodology for applying NFP. For all of our different modules or different zones, we’ll be using role-based access control, and secure management, and reporting.
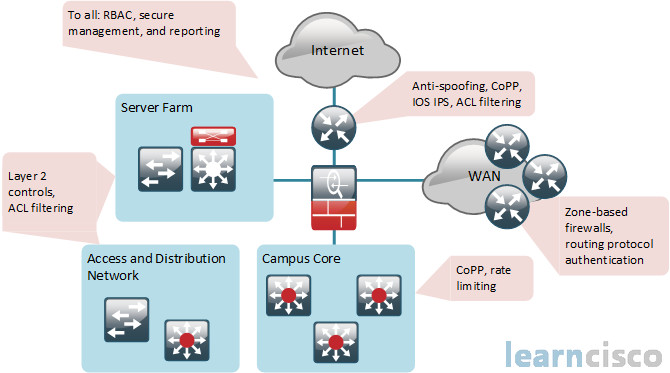
Moving around clockwise, at the Internet layer or the customer edge router, we’ll have antispoofing mechanisms, CoPP, IOS IPS, and ACL filtering access control lists. For the WAN, we can use zone-based policy firewalls and authentication of routing protocols. At the Campus Core, we have a lot less policy there but we can still have CoPP and rate limiting on those high speed multilayer switches. At the access distribution network and server farm or datacenter, we can have Layer 2 controls and ACL filtering.
What Cisco NFP does not consider
Now even though Network Foundation Protection is extremely powerful and it has a very feature rich toolset, there are some things it doesn’t consider. It can’t make up for poor network design, it can’t accommodate for a lack of physical security. It also doesn’t provide any High Availability, nor does it really contribute to your High Availability design. It also doesn’t come into play as far as your change management goes, and it’s not really part of a disaster recovery plan. These are really all separate aspects of your written security policy.
Our Recommended Premium CCNA Training Resources
These are the best CCNA training resources online:
Click Here to get the Cisco CCNA Gold Bootcamp, the most comprehensive and highest rated CCNA course online with a 4.8 star rating from over 30,000 public reviews. I recommend this as your primary study source to learn all the topics on the exam.

Want to take your practice tests to the next level? AlphaPreps purpose-built Cisco test engine has the largest question bank, adaptive questions, and advanced reporting which tells you exactly when you are ready to pass the real exam. Click here for your free trial.
