Now earlier we mentioned SecureX, and let’s define it. It’s an access control strategy, but the goal here is to give us some more effective higher level policy creation and enforcement, especially for mobile users connecting from anywhere, anytime, using any device. Now, Cisco SecureX will give us much more effective security and situational awareness because it uses a broad combination of parameters for its policy. Instead of a lot of the complex firewall rules, our security policy can now be based on the context. For instance, if a salesperson needs to get access to a global sales forecast from a smartphone in Japan through an unknown or unauthenticated protocol, the connection will be valid even if access was authenticated through the main campus in Indiana two hours before. This sort of policy enforcement uses next generation scanning components that are combined with the new Cisco SecureX architecture. This is the next-generation endpoint, and it allows us to automatically find the nearest scanning element located in the virtual security fabric to make our seamless connection. In our diagram, we see the components of the Cisco’s SecureX strategy.
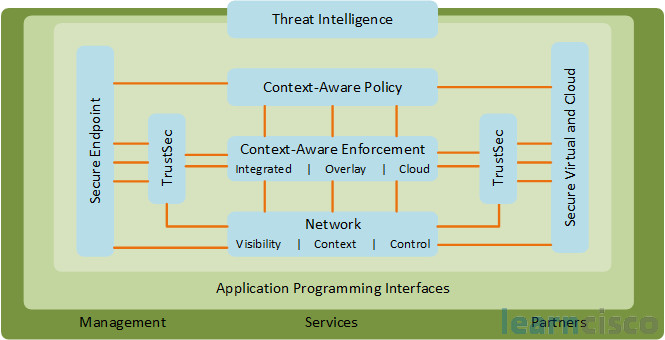
At the core is the context awareness, which allows things like firewalls, sensors, web proxies, and gateways, and other network devices – like routers and switches – to use data such as the identity of the user, and the security posture of the laptop, along with the point of access for the network and many other components to define the access policy. You’ve also got the Cisco AnyConnect Client, that’s our essential component that offers consistent user interface and consolidates traditional function specific client software into one single product.
There is also Cisco TrustSec. This functionality extends the access control capabilities end-to-end. It uses security group tagging to mark traffic and allow other network elements to the network to enforce policy. Cisco TrustSec will generate a distributed access policy enforcement mechanism that can optionally offer confidentiality using encryption technology.
Another important element is the Security Intelligence Operations (SIO). This is a cloud-based security service access to a web browser. It’s a global network of shared resources, software and data provided to Cisco customers, as well as devices on-demand. SIO is used for real-time insight into the global threat environment.
Context aware policies
Let’s talk more about context-aware policies through Cisco TrustSec. Cisco TrustSec is going to depend upon context awareness to enforce its policy and simultaneously offering flexibility and access control on a case-by-case basis. Traditional access control parameters, like user identity, are also considered and this is the base component where we’re determining our context. IEEE 802.1X is typically used to define the identities of those coming into the network, and so we’ll also consider non-authenticated devices – like IP phones, printers, and so forth – because we have capabilities with .1X. Other conditions will be gathered from the AnyConnect Client and an array of enforcement devices. So we could let an employee with high security clearance into the network during the weekdays, using an uninfected corporate laptop from a campus office wired network. However, this is in the same situation as allowing that same person to access the network from an unknown, possibly infected PC, at an Internet cafe. So to make such distinctions available to us in our policy and conditions is key to this TrustSec technology. In other words, the same person could be allowed into corporate resources with a broad access under certain conditions, but they may have to quarantine themselves and update their antivirus software, or unlock a user password in different situations. And so our network as a system will adapt to every scenario hypothetically.
Cisco SecureX Components
Here we see kind of an inventory of our Cisco SecureX components. Over on the left-hand side, we have the Cisco AnyConnect Client as well as the 802.1X supplicant.
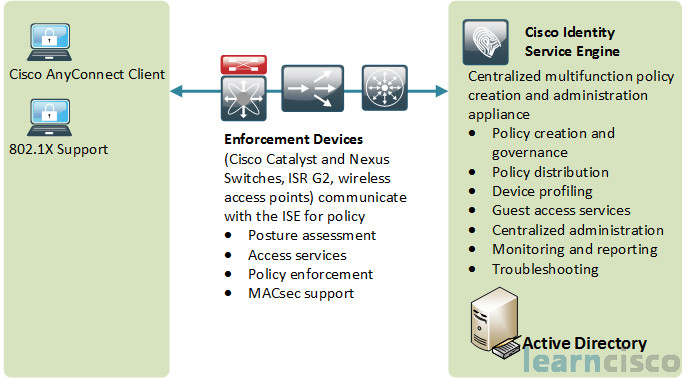
Then in the intermediate area is the enforcement device. You can also kind of call this the authenticator, which includes Cisco Catalyst and Nexus switches, Integrated Services Router Generation 2, wireless access points. And these can do posture assessment, access services, policy enforcement, and the MACsec support. That’s the encryption process providing confidentiality via MAC security. And then on the right-hand side, we have the Cisco identity services engine with its policy generation and governance, distribution of policy, profiling of devices, providing guest access services, centralized administration, monitoring and reporting, and troubleshooting. It also has the ability to integrate tightly with Microsoft’s Active Directory.
Cisco AnyConnect
The Cisco AnyConnect Client is actually officially called the Cisco AnyConnect Secure Mobility Solution. And this actually allows you to get more than just PC-based connectivity, it could also be a smartphone as well. It’s going to use SSL TLS or IPsec VPN to give you a seamless always on, always protected environment to the enduser. It also allows you to enforce policies and block malware if you want to leverage cloud-based or hybrid web security.
The Mobility Client is lightweight, it’s very modular, and it supports customizable capabilities. It has broad operating system support – Windows, Linux, mobile devices, smartphone, tablets (including Apple IOS, Windows mobile, Android, and others). Cisco AnyConnect provides an always on solution. It will find the nearest enforcement element, and it will apply multiple types of policies including SSL and IPsec VPN, 802.1X authentication and authorization, Network Admission Control (NAC) among others. By using this client, you can implement your DLP (Data Loss Prevention), your threat prevention, AUP (Acceptable Use Policies), as well as access control mechanisms – all in one lightweight client.
Cisco TrustSec function explained
Let’s take a look at how Cisco TrustSec provides a secure resource Security Group Access or SGA. It’s going to restrict a user with this SGA feature.
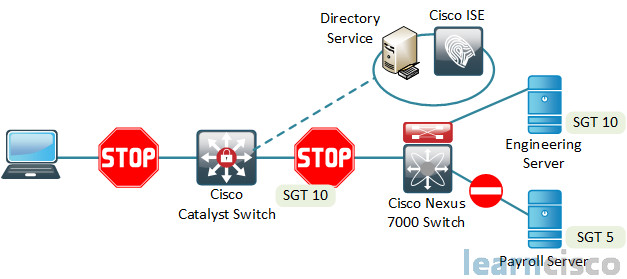
So over here on the left we have, let’s say Alice, who is a full-time employee, she is in engineering, she is using wireless access from a laptop, and it’s 8 o’clock in the morning. As she connects to this catalyst multilayer switch, she is going to be stopped. The switch will identify her as a user and request authentication. The user will be authenticated against the ISE, and it will provide access policy. Then over to the right, the domain controller resources will be tagged with a particular role. Then the Nexus 7000 switch will read the SGT (the Security Group Tag) and enforce the access policy. Then the user traffic is tagged with the user role, again back on the Cisco catalyst switch. So the SGA will read and enforce policy tags on a TrustSec-enabled switch along the data path using security group ACLs or SG ACLs. And really, ultimately what’ll happen finally is TrustSec will provide data confidentiality, this is known as MACsec. For instance, a policy might demand that any employee from the finance department who accesses the payroll server has to have their data secure. TrustSec understands this policy, and then will redirect the network to dynamically encrypt the data of that user.
Our Recommended Premium CCNA Training Resources
These are the best CCNA training resources online:
Click Here to get the Cisco CCNA Gold Bootcamp, the most comprehensive and highest rated CCNA course online with a 4.8 star rating from over 30,000 public reviews. I recommend this as your primary study source to learn all the topics on the exam.

Want to take your practice tests to the next level? AlphaPreps purpose-built Cisco test engine has the largest question bank, adaptive questions, and advanced reporting which tells you exactly when you are ready to pass the real exam. Click here for your free trial.
