Let’s explore the secure network life cycle management, and we want to focus on what we’re doing today as opposed to the way things were done in the past.
Risk, compliance, and security
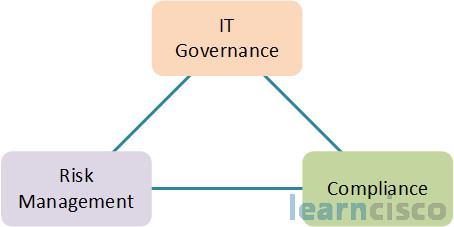
In the past, we kind of combined IT governance, and risk management, and compliance, separated within business units or organizations – maybe even by the type of regulation they’re under. You had a lot of unidentified risks, you had a lot of redundancies, and then you had higher cost.
Today, we’re going to integrate this organization wide. So every business unit, every component of the organization is under IT governance, it’s under risk management, it’s under compliance. This is going to avoid any conflicts, it’s going to avoid gaps, okay, it will avoid wasteful overlaps or redundancies. It’ll actually improve our operational decision-making, our strategic planning, and it’ll add business value. And of course, it makes IT security part of the strategic initiative of your organization – either public or private. This convergence will give us an ideal framework and context to generate a life-cycle approach to information security.
Secure network life cycle
Here is a diagram that shows our secure network life cycle. At the center of this, of course, is our converged security policy, which dictates our IT governance, risk management, and compliance. There are five phases we’re going to talk about here starting with the initiation phase, then the acquisition and development phase, followed by the implementation phase. Then step four is the operations and management phase, and then step five – the disposition phase. Each of these five phases has a kind of a minimum required set of steps that you have to effectively incorporate into your development system. And basically, in the context of IINS here, our system would be the network.
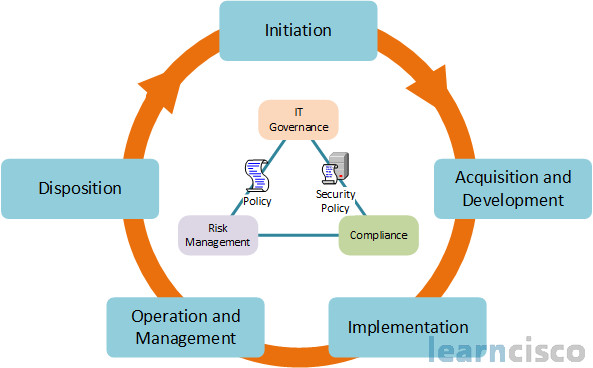
Okay, let’s break down the functionality of these five different phases. In the initiation phase – this is typically the information gathering phase – you’re going to categorize your security into different levels – maybe three levels: low, moderate, or high. You may also categorize different areas of your network based on the value of the assets there. That could come into play if you’re going to leverage this with your Cisco IPS implementation, and your risk ratings, your TLVs. So here you want to delineate the potential impact on CIA (Confidentiality, Integrity, and Availability). You’ll also do the preliminary risk assessment – the initial description of the needs of your system, also defining the threat environment where your system operates. Of course, when we talk about our system, we’re talking about our networking components.
The acquisition and development phase is very important. This is where you’re going to your full-blown risk assessment and risk analysis. You’ll also do your security functional requirement analysis, okay – what are the components, what is your system security environment, for example what is your existing enterprise security policy, and security architecture, and functional requirements. You’ll also look at assurance requirements – are you under any legal mandate, are you under HIPAA, are you under Sarbanes-Oxley or Department of Defense, is there any kind of assurance that needs to be taken into consideration. You’ll also consider cost and budgeting here, you’ll also generate a bunch of reports for all of the stakeholders. You’ll do your full-blown security planning in this phase as well and you’ll have supporting documentation for that security planning, and you’ll develop your security controls – your technical controls, your administrative controls, your physical controls. You’ll also develop security testing and evaluation processes, maybe do some penetration testing and auditing. You’ll have other planning components as well.
The next phase – the third phase – is the implementation phase. This is where you’re going to do inspection and acceptance of your hardware and software solutions, and your system functionality solutions. You’ll explore the system integration and how all these components work together. You want to look at deployment and configuration, also security certification. You may be looking for known vulnerabilities in your existing hardware and software solutions. Make sure that you’re certified and accredited, this is where it really happens in this phase.
The fourth phase is the operations and maintenance phase. This is really where a lot of us are going to be doing some of our first kind of CCNA security activities. This is the configuration management, and configuration control, and continuous monitoring. This is where we have our continual improvement, ongoing operational maintenance. The day-to-day activities happen in this fourth phase.
The final phase is the disposition phase where you’re going to determine what information and data are you going to preserve, what systems have to be preserved for how long, based on governance, based on your mandates. You also might be sanitizing media – deleting, erasing, and writing over data when necessary on hard drives and removable drives. Also, the disposal of hardware and software based on your security policy. Those are the five phases, got to memorize. You got to have a good idea of what goes on in each of the five phases.
Now this five-phased approach didn’t come in a vacuum, and it’s not really Cisco’s idea. It’s based on NIST, the NIST organization – National Institute of Standards and Technology. It’s actually based on publication 800-64 revision 2. So you can see here different frameworks. This is the one we’re going with, the one at the bottom.
| Framework | Strengths | Focus |
|---|---|---|
| COBIT – Control Objectives for Information and Related Technology | – IT controls – IT metrics |
– IT governance – Audit |
| ISO 27000 series (supersedes ISO 17799 and BS7799) | – Global acceptance – Certification – Security control |
– Information security management system |
| ITIL – Information Technology Infrastructure Library | – Processes – Certification |
– IT service management |
| NIST – National Institute of Standards and Technology, 800 Series | – Detailed, granular – Tiered controls – Available for free |
– Information systems – FISMA (federal government) |
It’s detailed, it’s granular, it has tiered controls, it’s freely available, and it’s focused on information systems and federal government systems. There are other frameworks though – there is COBIT, there is ISO 27000, there is also the ITIL, which I mentioned earlier. You may be under one of these other frameworks in your organization, so you need to be aware of that.
Assessment phases of the cycle
What we see here is some of the most important actions we have to take in order to determine the ability to detect, defend, and respond to network attacks.
- Vulnerability assessment
- Internal assessment
- External assessment
- Access network assessment
- Operating system and application assessment
- Security posture assessment and documentation
We have to have our security posture assessment – which is the first step in planning – our security solutions, we need to do an internal assessment. We focus so much on threats coming from the outside that we forget to think about threats that emanate from the inside – either structured or unstructured, malicious or accidental – so internal assessment. Also, of course, external assessment to see what’s coming through our perimeter routers in our perimeter firewall systems. Wireless assessment – do you have a wireless network, is your wireless network only a guest VLAN, are you providing wireless solutions for your corporate LAN as well, very important. Also, security posture assessment, analysis, and documentation. Documentation in the form of reporting, and metrics, and graphs, technical details using topological maps through things like Microsoft Visio, for example. These are extremely important in assessing your security posture – knowing where things are, knowing where your critical assets are, and knowing how they’re connected.
Our Recommended Premium CCNA Training Resources
These are the best CCNA training resources online:
Click Here to get the Cisco CCNA Gold Bootcamp, the most comprehensive and highest rated CCNA course online with a 4.8 star rating from over 30,000 public reviews. I recommend this as your primary study source to learn all the topics on the exam.

Want to take your practice tests to the next level? AlphaPreps purpose-built Cisco test engine has the largest question bank, adaptive questions, and advanced reporting which tells you exactly when you are ready to pass the real exam. Click here for your free trial.
