ERR_SSL_WEAK_SERVER_EPHEMERAL_DH_KEY
Yeah, this is one of the new features coming with the latest version of Google Chrome (45). It basically means that the most used browser is becoming unusable to manage older Cisco products. I faced the problem when I was trying to access one CUCM version 9.x in my lab.
I’m pretty sure there are thousands of products working pretty fine sitting in your private LAN behind a firewall, but you simply cannot use Chrome to access them as all of them require https. I’ve spent probably half a day looking for a workaround in Chrome but so far I wasn’t able to find such.
{{adaptive}}
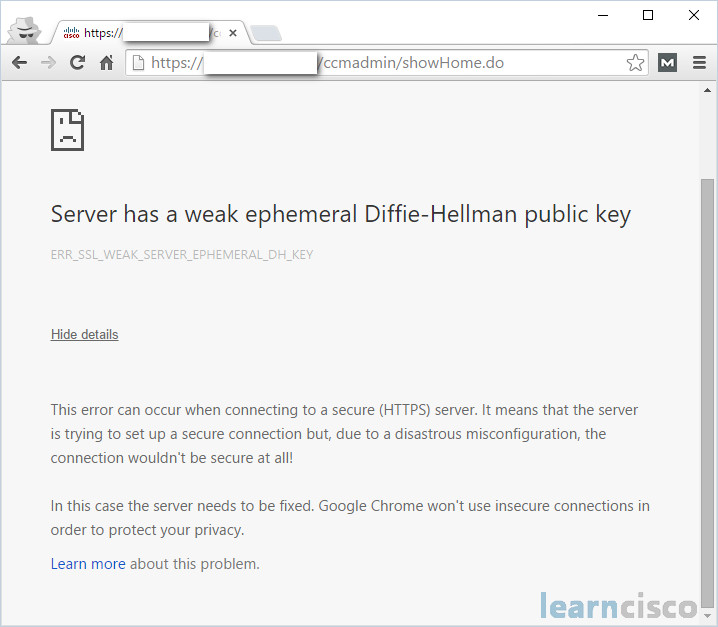
The message in the browser is saying “This error can occur when connecting to a secure (HTTPS) server. It means that the server is trying to set up a secure connection but, due to a disastrous misconfiguration, the connection wouldn’t be secure at all! In this case the server needs to be fixed. Google Chrome won’t use insecure connections in order to protect your privacy.” There is even a link with more instructions about how to fix the problem but all of them are asking you to do the changes on the server side. Well, thanks for that but I simply cannot do it, as Cisco’s back end is pretty much closed for changes. Honestly, I think this time Google overdid it!
The “fix” in the browser is related to a well known security attack called Logjam. You can find more details about it here (https://weakdh.org/).
Workaround for Google Chrome
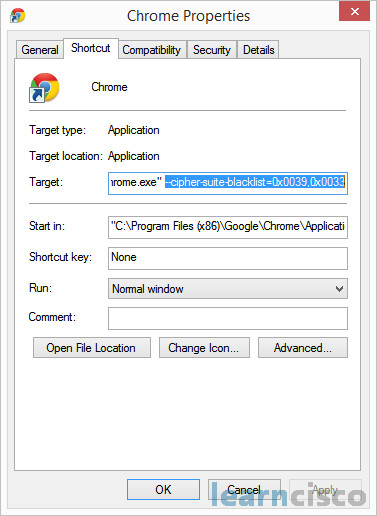
So, you have some old Cisco product that you cannot access with Google Chrome. What to do now? You have to create new shortcut for your Chrome adding the following startup parameter:
“C:Program Files (x86)GoogleChromeApplicationchrome.exe” –cipher-suite-blacklist=0x0039,0x0033
By doing this you are allowing the weak Diffie-Hellman public keys – TLS_DHE_RSA_WITH_AES_128_CBC_SHA (0x33) and TLS_DHE_RSA_WITH_AES_256_CBC_SHA (0x39) which is absolutely enough to be able to access your Cisco environment with Google Chrome.
{{adaptive}}
Workaround for Mozilla Firefox
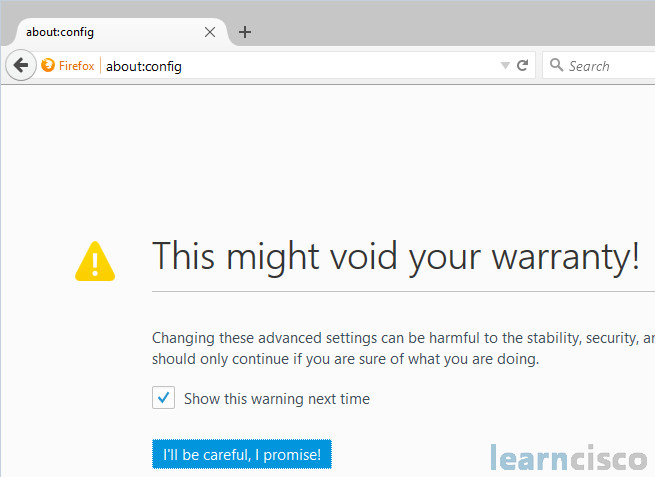
When I switched from Firefox to Chrome as a primary browser couple of years ago, I did it with some reserves. And here it comes probably the biggest proof that Firefox is much more mature browser. Mozilla Firefox has the same fix (Error code: ssl_error_weak_server_ephemeral_dh_key) as Google Chrome and it was even released couple of weeks earlier but together with that there is a workaround by modifying some of the advanced settings. Here is a step-by-step guide of how to do that.
Open your Firefox and type in the address bar about:config. There will be a warning message so you will have to promise that you will be careful.
Once you open the advanced configuration section, type in the Search field ssl3. Change the values of security.ssl3.dhe_rsa_aes_128_sha and security.ssl3.dhe_rsa_aes_256_sha from true to false by simply double clicking on them.
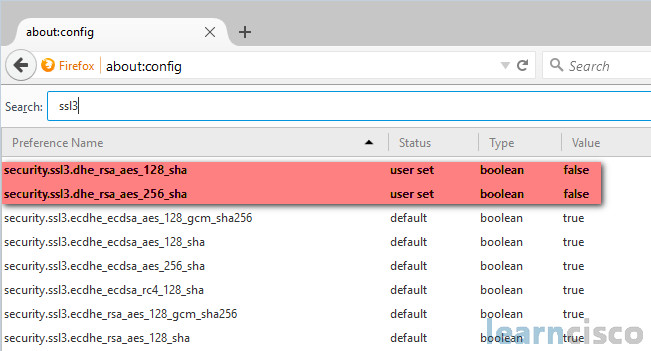
That’s it! Now you can use Firefox to access your devices which are still running weak Diffie-Hellman ciphers.
Our Recommended Premium CCNA Training Resources
These are the best CCNA training resources online:
Click Here to get the Cisco CCNA Gold Bootcamp, the most comprehensive and highest rated CCNA course online with a 4.8 star rating from over 30,000 public reviews. I recommend this as your primary study source to learn all the topics on the exam.

Want to take your practice tests to the next level? AlphaPreps purpose-built Cisco test engine has the largest question bank, adaptive questions, and advanced reporting which tells you exactly when you are ready to pass the real exam. Click here for your free trial.
